Optable Blog
Learn about the modern advertising landscape and how Optable's solutions can help your business.
CTV ad spend is growing, but most publishers aren't capturing their share. Without a robust identity infrastructure, publishers can’t monetize their rich audience data at a premium price, connect their audiences to valuable signals or transaction data, or transact at the speed the market now demands.
Two Distinct Identity Challenges
CTV poses two unique challenges: siloed data and unauthenticated data. Without a clear idea of who their users are, CTV platforms can’t accurately resolve identity, create addressable audiences, or implement agentic workflows.
For premium streaming publishers, broadcaster apps, and subscription video services, rich data is available. Viewers have logged in with their own accounts, but this login data sits in separate systems that don't talk to each other. A major media company might have authenticated viewer data in a news app, TV streaming app, and magazine subscriptions with no connection between them. Advertisers can't reach the same person across properties because the publisher's systems don't recognize it's the same person.
For free, ad-supported streaming (FAST) publishers, the situation is different. No login is required means no email address and no account data. With device ID or household IP, identity resolution becomes more difficult. A viewer watching a free channel on Roku or a Samsung TV is effectively anonymous to the ad system, even if they sit in a household with a known address, purchasing history, and browsing behavior on other devices.
Both problems cost publishers money. The solutions are related but distinct, and an identity infrastructure worth building needs to handle both.
Why the Web Playbook Doesn't Translate to CTV
Publishers who approach CTV with web-based tooling quickly realize that the methods that work in a browser don't function in a streaming environment.
The tag-based approaches that most web identity infrastructure uses don't apply. Identity resolution on CTV has to happen server-side, which is a meaningfully higher technical lift than adding a script to a web page.
The identifier landscape compounds this. The signals that exist across streaming platforms come in different forms and don't naturally connect: Roku IDs, Samsung TV device identifiers, Fire TV device IDs, household IP addresses, and hashed email addresses all live in separate environments.
The household IP is the most useful signal available for FAST audiences. A household that watches free content and visits the publisher's web properties can be linked via residential IP. Adding web behavioral data makes the inferred CTV profile much stronger.
Solving CTV identity in isolation tends to undervalue what publishers already have access to. A publisher whose CTV data lives separately from their web and mobile data surrenders targeting precision and remains invisible to the automated systems buyers are already using to discover and activate against publisher inventory.
What CTV Identity Infrastructure Needs
The underlying infrastructure needed is the same regardless of which problem a publisher is trying to address.
Both require a server-side resolution layer that evaluates available identifiers for a given impression and selects the strongest one in real time. That selection happens automatically, with consent and privacy enforcement built into the workflow. Publishers can then directly connect to CTV-specific ad servers and SSPs including Publica, Freewheel, and Magnite.
Publishers with siloed authenticated data need to resolve the same viewer's identity across sources, including:
- TV streaming and VOD apps
- News apps
- Magazine subscriptions
- Web properties
Publishers with unauthenticated inventory need to make inferences about their users to get a clearer idea of who they are. The path is straightforward:
- Collect Household IP addresses and device identifiers from the streaming environment
- Map these identifies to email addresses through data partnerships
- Translate them into alternative IDs the programmatic ecosystem recognizes
- Share the resolved identifiers to the ad server without ever needing an email
The same identity foundation should handle both resolution paths. Agentic audience workflows require a single, queryable graph to function. A fragmented infrastructure can only ever propose partial audiences, and partial audiences don't win briefs.
The Agentic Payoff
Identity resolution is the prerequisite for unlocking agentic revenue opportunities. The payoff becomes possible when publishers don’t have to rely on manual audience packaging and activation. Agentic workflows enable efficiencies and opportunities, including:
Local Household Targeting
Connecting household-level identity to geographic and behavioral signals creates high-value inventory packages for local and regional advertisers. But the audiences need to be continuously refreshed as new viewing data comes in, and manually matching them to incoming briefs at scale isn't viable.
Optable’s Audience Agent reads an incoming brief, queries the identity graph for matching households, builds the audience, and routes activation through integrated SSPs. A workflow that previously required a data analyst and a campaign manager now completes in minutes.
Content Alignment
Publishers with strong editorial signals can command a premium by matching advertiser brand requirements to specific content environments. Performing that analysis across a large CTV catalog and keeping it current requires automation.
Optable’s lightweight SDK continuously collects and organizes your 1P data, giving the Audience Agent up-to-date information for audience discovery, packaging, and activation.
Addressable FAST Inventory
FAST publishers have large impression volumes and low baseline addressability, meaning even modest resolution rates produce meaningful revenue. Because those audiences are built from inferred signals rather than deterministic data, they need to be rebuilt continuously as viewing behavior changes.
Optable's Audience Agent uses content context and behavioral signals to construct audience packages that give buyers a credible reason to pay a premium on inventory they might otherwise overlook.
Across all three applications, the practical effect is the same: publishers with lean teams can handle more volume, respond to briefs more quickly, and offer more customized proposals without adding headcount.
CTV Revenue Begins With Identity
Publishers with siloed authenticated data need to connect what they already have. FAST publishers need to build from the signals they have available. These starting points converge on the same outcome: a unified identity and audience infrastructure that spans every environment where viewers show up, in a format that buyers and buyer agents can act on.
Publishers need a robust identity infrastructure to build addressable audiences, manage ad frequency across devices, close the measurement loop, and participate meaningfully in the emerging agentic ecosystem. The identity work done today determines which publisher inventory is visible to buyer systems tomorrow.
Ready to build an identity foundation for the agentic era? Schedule a demo today.
More RFPs mean more deal opportunities, but for leaner Ad Ops teams, meeting advertisers’ rising expectations can be increasingly difficult. Advertisers are increasingly looking for personalized, unique approaches to their RFPs.
Manually responding to an RFP takes too long to keep up with those time-sensitive demands, especially when advertisers are using buyer agents to query your inventory.
The Cost of a Slow RFP Response
Unanswered RFPs leave money on the table. The manual response process doesn’t meet the market’s demands for volume, speed, and specificity.
The impact of slow responses extends beyond fumbling isolated deals:
- Lean Ad Ops teams are faced with higher volumes of incoming RFPs, increasing the gap between demand and bandwidth.
- Publishers responding under pressure tend to default to familiar, broad segments, resulting in undifferentiated proposals to buyers who expect precision.
- Teams that are at capacity may sideline incoming RFPs, which registers only as unanswered briefs instead of lost revenue.
- Advertisers may deprioritize publishers who don’t respond with audience recommendations at the pace and depth they’ve come to expect from walled gardens.
- As more advertisers deploy buyer agents to search for inventory, a manual workflow has no answer for a buyer agent querying your inventory outside business hours.
The solution isn’t just to speed up the process but to improve the specificity of audience proposals. Agentic workflows supported by platforms like Optable make it possible to surface audiences that manual processes routinely miss and close the loop from RFP to activation without the bottlenecks.
How Agentic Workflows Are Changing the Sales Process
No matter how good the team is, a manual RFP workflow limits how many briefs they can strategically answer in a day. Agentic workflows remove that cap by changing what happens at each stage of the sales process.
When a brief arrives, instead of routing it to a queue and waiting for a data analyst to pull segments, the agentic workflow begins immediately. An agent can read the brief, extract campaign goals, and generate audience recommendations using the publisher’s enriched first-party data. Publishers with low or declining traffic can more effectively monetize their audiences when an agent surfaces precise, differentiated segments to target.
This process surfaces segments that a manual query would overlook: niche behavioral combinations, trait correlations, and audience overlaps that only become visible when systematically searching the full depth of the data. Optable's Audience Agent handles this step, proposing ranked segments with confidence scores and reach estimates that give the sales team something to review rather than build from scratch.
The team can adjust in natural language to instantly update the recommendations. A human reviews before anything activates, keeping the publisher in control of what goes out and to whom. Then, the agent can generate a response draft and activate audiences directly across ad servers and SSPs. The proposal, complete with audience definitions, reach estimates, and pricing, is ready to send in a fraction of the time.
Agentic workflows also change how buyers and sellers interact. As agencies and brands increasingly deploy buyer agents to search for inventory, publishers who aren't visible to those systems are out of consideration. A Sales Agent like Optable’s allows publishers to define their audience products, configure pricing and access rules, and make that inventory automatically discoverable and transactable to buyer agents querying for relevant audiences.
Publishers with premium audiences get access to more deals, and buyers receive a structured proposal mapped to their brief.
What Your Team Can Do With the Time Back
When proposal building stops eating up your team’s bandwidth, the work that requires human judgment gets the attention it deserves. For Ad Ops teams, that looks like:
- More thorough campaign analysis: With a tool like Optable’s Audience Agent handling brief intake and segment recommendations, teams can focus on surfacing compelling insights around their advertiser’ audience to build smarter packages around performance instead of availability.
- More niche, addressable audience products: With agentic support, teams can develop more compelling audience products that go beyond standard segments without allocating more resources to surface them.
- Unique, custom creative approaches: Brands aren’t looking for cookie cutter proposals. They want to see platforms with custom audiences built from unique first-party data that aligns with their vision, and agentic solutions give Ad Ops teams the time and ability to deliver.
- The ability to answer more briefs: Lean teams can address briefs that they previously would have deprioritized or overlooked due to bandwidth constraints, increasing revenue potential without expanding headcount.
- Stronger advertiser relationships: Teams that aren’t weighed down with manual processes have more time for data collaboration with buyers. Sharing audience insights, validating campaign fit, and collaborating on strategy builds transparency that fosters a long-term partnership.
Agents help relieve the mechanical burden of processing and responding to RFPs so your team can focus on more meaningful tasks that require creativity, strategy, and human judgment.
Win More Deals With Smarter Workflows
Ad Ops teams with the right infrastructure to support them can respond faster, propose better audiences, and build stronger advertiser relationships without working harder.
Agentic workflows change what a lean Ad Ops team can accomplish in a day: more brief responses, more precise audiences, and more time for the strategic work that turns one campaign into a long-term relationship.
Every brief the agent handles well is data that informs the next one. Every niche audience that wins a deal becomes part of a stronger audience product portfolio.
The buying landscape is moving toward greater automation on all sides. Publishers building agentic infrastructure are positioned to compete in that environment and won’t have to scramble to catch up.
Optable gives publisher teams the agentic infrastructure to do exactly that, from RFP intake and audience activation to outbound discoverability. Ready to see it in action? Schedule a demo.
We returned to the Beeler.Tech Navigator event this year to join fellow industry leaders in conversations about latent data, signal quality, practical AI applications, and more. Optable’s Director of Sales, Kristy Schafer, led a session with Tim Hurd, VP of Media at Goodway Group, to share how the agency rebuilt their audience stack.
That initiative produced Passport One, Goodway’s proprietary data and intelligence layer that centralizes audience creation and decisioning with the ability to activate across the ecosystem. Optable provides the identity, audience, and collaboration layer where clients onboard first-party data and Goodway centralizes its enterprise data partnerships.


What Goodway Built
The motivation was straightforward. Goodway wanted a system that allowed them to centralize audience creation and decisioning with the ability to activate across the ecosystem.
In practice, that resulted in:
- Client data onboarding dropped from four weeks to roughly five minutes.
- The data fees stacked into every activation came down.
- More spend now routes directly to the source: the publishers themselves.
- Planners can index and overlap consumer segments to hit multiple consumer profiles with more strategic impression targeting.
The goal throughout: more value out of every working dollar, with more of that revenue passing through to the content owner.
Why They Built It
Tim spent meaningful time on the why behind the work. Goodway's clients aren't simple. A single brand often needs to reach multiple consumer personas at once, against very different media outcomes across awareness, in-store visits, and new account creation.
That kind of complexity demands a centralized audience layer, where the same audience can be pushed out to a multitude of destinations rather than rebuilt for each one. His point landed cleanly: the more easily publishers can plug into that workflow, the easier it becomes to spend with them.
What This Means for Publishers
Asked what he most wants from publishers going forward, Tim was direct. He hopes publishers will build similar infrastructure on their side in the form of interoperable audience platforms.
The next phase on this journey is agent readiness. As both buyer- and seller-side agents evolve, publishers with a strong identity and audience layer will be the ones surfacing inside the agency's buying strategy.
Agencies will gain the ability to build audience strategies across publishers using the underlying metadata of each one's identity and audience infrastructure. In turn publishers can better monetize their first-party data while still allowing the agency to buy at scale from one centralized location.
What Happened to CPMs?
The question that probably mattered most to the audience came from a publisher in the room: what's happened to CPMs through all of this?
Tim's answer: CPMs have come down. The agency gets the efficiency it set out to capture, and more of that working media is now flowing straight to the publisher instead of being absorbed by the middle.
The broader upside for publishers willing to evolve in this direction:
- Less ad-tech in the way
- More paths to buying
- Broader inclusion in plans
That dynamic is exactly the upside Tim's pitch holds out for publishers willing to evolve in the direction he's describing.
He closed with a line that captured the whole posture:
"Democratize data access, and look at each other less as competitors and more as a cohort."
Why Identity Is Key to the Agentic Revenue Engine
As the agentic era takes off, publishers and advertisers are looking to enable and implement intelligent workflows for adtech use cases. At the same time, third-party identifiers continue to decline, so publishers are motivated to stop relying on external signals and start building and activating their own direct audience data. The solution positioned to allow publishers to leverage new AI-powered agents and turn first-party data into their most durable asset is the identity graph.
Agentic solutions generally connect to data from a variety of sources, including first-party, partner integrations, and contextual or 3rd party signals. While the latter two sources have some influence on AI-powered results, the richer, more accurate, and more detailed your first-party data is, the more you can control and improve the outcomes from your AI agents.
Additionally, as signals such as third-party identifiers (including device identifiers and IP addresses) decline or become inconsistently available, audience addressability is undergoing a fundamental shift. You can no longer rely on free, third-party signals. Instead, high-quality audience data and addressability now depend on direct, privacy-first audience relationships that build trust and prioritize data security and consent.
The identity graph sits at the center of this double transformation, feeding high-quality data to agentic tools while also enabling publishers to recognize audiences across channels and activate them in privacy-safe ways. Strategically activating your ID graph unlocks revenue opportunities that enhance and extend beyond programmatic advertising.
What an ID Graph Really Unlocks
Your ID graph becomes the connective tissue between your data, your partners, and your revenue strategies, as well as the core intelligence that powers your agentic solutions. By linking identifiers such as hashed emails, device IDs, login IDs, contextual signals, and more, publishers can use identity graphs to build up a unified view of their audiences across web, mobile, CTV, and in-app environments.
This unified view allows you to:
- Empower AI-powered audience planning and activation
- Increase addressability without having to rely on third-party cookies
- Improve match rates with key partners (SSPs, DMPs, CDPs)
- Enrich inventory with high-value audience signals
- Maintain transparency, consent, and privacy controls
A robust ID graph transforms fragmented data into a powerful tool for monetization, measurement, collaboration, and operational efficiency. Here’s how to ensure your identity strategy is scalable and aligned with business objectives for long-term success.
Step 1: Align Your Teams around a Strong Identity Strategy
Before they can achieve any kind of successful activation, publisher organizations need to set clear goals and coordinate across teams and functions.
Assemble a Cross-Functional Workgroup
Identity-related projects require coordination with multiple teams across a publisher’s business, including ad operations, data analysts, developers, and legal teams. A cross-functional workgroup ensures alignment on compliance requirements, use case prioritization, and execution.
Define Success for Your Organization
Whether it’s increasing bid CPMs through enrichment or launching new authentication strategies, every initiative must have well-defined, measurable success markers. Correlate these goals with clear tracking methodologies to ensure progress and accountability. Depending on where you intend to move the needle, you may need to consider custom tooling for effective tracking and attribution.
Connect Goals to Measurable KPIs
Tie your goals to measurable KPIs such as match rate improvement, authentication growth, and time-to-integration for new partners. KPIs will largely fall into four primary categories: monetization and revenue; data and identity strategy; campaign performance and measurement; and operational efficiency.
Respect Regulations and Requirements
Privacy regulations vary by location (e.g., GDPR, CCPA), so your identity solution must account for consent preferences and legal restrictions no matter where your audience is located. Implement transparent data collection practices, and use consent management platforms (CMPs) where necessary to increase trust with advertisers and audiences.
Step 2: Audit Your Data and Identify Gaps
Our report with Digiday on the state of audience data monetization found that 50% of publishers are limited by decentralized data. So once you set your goals, your next step is to understand and manage your current data landscape. Identify gaps that limit addressability by auditing where data lives and how it’s collected, stored, and activated.
- Map your entire data ecosystem so you can see where your data is stored and what tools manage it. Critically, the mapping process will also help you identify data silos and create a strategy for integrating that data into a unified, central repository.
- Include both first-party and third-party identifiers in your data audit, with a focus on deterministic, high-quality signals like authenticated user IDs and hashed emails.
- Determine how much of your audience is covered by first-party identifiers. Uncovering how much is invisible in identity gaps will guide key decisions around authentication strategies and enrichment partners.
Step 3: Expand and Strengthen Authentication
As shared third-party IDs become less reliable and readily available, authentication becomes the backbone of a durable identity graph. Unfortunately, most publishers have a comparatively low percentage of authenticated users, which decreases the value of their inventory. Capturing reliable, authenticated identifiers results in better targeting, stronger audience insights, improved measurement, and higher confidence for advertisers.
Publishers need to focus on expanding authentication to unlock more reliable identifiers and increase the value of their identity graphs. Effective strategies for authenticating users include offering email subscriptions, premium content or membership models, platform-based logins, and engagement-driven experiences such as newsletters, contests, or gated content. Each interaction across these authentication channels strengthens first-party data and improves the ability to recognize users in decreasing cookie environments, creating more opportunities for effective advertising.
Step 4: Maximize ROI through Well-Defined Use Cases
While an identity graph is an important tool, what matters most for driving revenue is how effectively you leverage it. By defining the key use cases that will allow you to maximize return on investment, you can transform your ID graph into a competitive advantage, increasing competition for inventory, improving match rates with identity frameworks, and driving higher CPMs.
Programmatic monetization or direct ad sales are often the first places publishers see returns from identity activation. By adding valuable data signals such as user intent or first-party insights, you can offer advertisers opportunities for more precise targeting and maximized reach, which improves bid value for your inventory.
Additionally, a robust ID graph allows you to create high-quality, anonymized audiences or segments to either offer to advertisers at premium pricing or to sell on data marketplaces. You can also collaborate with advertisers to align inventory and data with their goals, so you can offer differentiated, enriched segments and high impact, custom ad opportunities that drive better results.
In short, the work of developing audiences with your first-party data and a strong identity foundation pays off in increased bid values, improved addressability, and new revenue streams.
Building on Programmatic: Where Real Growth Happens
Programmatic advertising remains the foundation of revenue for publishers, but it can be leveraged for even greater returns through agentic advertising tools in the age of AI. A well-composed ID graph is positioned to be the key foundation for agentic success, evolving programmatic into a more data-driven, less manual process that yields better results for publishers and advertisers alike.
Agentic solutions can act as AI-powered co-pilots for your sales teams, automating workflows and audience segmentation. But an AI agent is only as good as the data it uses. That’s why an identity graph built on curated first-party data remains the key for futureproofing your advertising strategy and achieving sustainable growth now and in the agentic era.
Audience-Based Direct Deals and AI-Ready Workflows
With a robust ID graph, publishers can connect a tool like Optable’s Audience Agent and use AI to package first-party audiences into premium, audience-based deals. ID graphs provide the governed data foundation that autonomous systems need to shorten time from planning to activation, accelerating RFP response times, scaling operations, and growing revenue in the agentic era.
Centralized identity data streamlines manual processes. It helps you leverage agentic solutions to reveal hidden audiences, analyzing every signal across all your data sources. It also uncovers previously unseen audiences within your identity graph, turning overlooked segments into valuable revenue opportunities. You can then market these segments to advertisers as a new, powerful way to reach qualified audiences at scale, commanding higher demand, fill rates, and revenue.
Audience Enrichment and Premium Pricing
Identity graphs are a foundation for enrichment opportunities with trusted data partners. Publishers can enable more precise targeting for advertisers by working with a data partner to bridge identity gaps across devices and platforms. This increases addressability and activates more precise targeting, ensuring seamless audience recognition in both authenticated and anonymous environments for improved campaign performance. More precise targeting equals improved campaign performance, which results in strong, long-term advertiser relationships and revenue growth for publishers.
You can also enrich your first-party audiences with third-party demographic, behavioral, or intent-based attributes. Optable Attributes allows you to enrich your audience footprint with additional audience data. The increased granularity of audience segments lets you create new and compelling ad packages for advertisers. An enriched audience built on a well-composed ID graph enhances ad relevance, driving higher engagement and performance. The ability to produce these kinds of measurable results for advertisers then leads to opportunities to sell your inventory at premium pricing.
Data Clean Room Collaboration
Today, three out of four publishers and advertisers view clean rooms for collaboration as important to their monetization strategy (source: Digiday Report). Clean rooms work hand-in-hand with identity graphs by enabling anonymized data matching across publisher identity graphs and advertiser datasets, providing a privacy-safe way for advertisers, agencies, and partners to match and analyze audiences for planning, activation, and measurement. This allows for custom audience planning, more accurate attribution, and transparent measurement, all resulting in high-value campaigns that can drive premium deals with advertising and publishing partners.
The Globe and Mail partnered with Optable to run direct campaigns via clean rooms and achieved 3.4x greater reach, 2.5x lower cost per reach, and 1.5x higher viewable impression efficiency. Read the case study here.
New Monetization Opportunities
Identity graphs can open doors to non-traditional revenue streams. As a publisher, you have unique insights into your audience that can provide incredible value to other publishers and advertisers. For example, your robust ID graph can be licensed to other organizations so they can leverage it in tandem with their first-party data for expanded reach and improved targeting. You can also build cooperative partnerships with fellow publishers by combining your respective ID graphs in a privacy-safe manner so as to improve reach and revenue opportunities for you both.
Turn Identity into a Competitive Advantage with Optable
The simultaneous shift away from third-party identifiers and towards agentic solutions offers publishers a unique opportunity. Investing in, building up, and activating your own ID graph means you can feed the highest quality data into emerging AI tools. You can then leverage AI to expand addressability, deepen advertiser relationships, and unlock new revenue streams by expanding the accuracy and reach of traditional programmatic advertising. The ability to securely connect, activate, and collaborate around audience data is what will drive long-term growth in the agentic era.
Activating your ID graph should be an ongoing strategy that evolves with regulations, technology shifts, and advertiser expectations. You need an intelligent platform that helps you assemble an identity graph across all your sources, enrich it with partner data sets, and activate it in all the channels that matter most for your business.
Optable is purpose-built to help publishers and their partners activate their identity data and drive smarter, more relevant, and more profitable advertising. Optable Audience Agent frees you from manual, human-mediated workflows and facilitates intelligent agent-to-agent collaboration that accelerates execution, reduces complexity, and drives better outcomes. We provide the open and interoperable infrastructure you need for secure, policy-governed data activation in the age of AI.
Ready to activate your ID graph for the agentic era? Contact our team to learn more.
Google algorithm updates have contributed to traffic fluctuations for years. Now, declines are even more rampant as AI-generated answers absorb search intent and social platforms deprioritize publisher content.
There’s the instinct to chase traffic volume with more content, increased optimization efforts, and broader distribution plans. In the past, this approach may have been enough to regain lost traffic, but volume alone isn’t going to solve your audience monetization problem.
The more urgent question to address is what you’re doing with the audience you already have. The publishers who can recognize, enrich, and monetize their unique visitors are better off than those who prioritize traffic volume alone.
This is the first of several posts inspired by the challenges highlighted during the 2026 Digiday Publishing Summit. Revisit the blog soon for more insights.
Traffic Volume Isn’t Your Best Asset; Your Audience Is
The simple truth is that audience addressability matters more than traffic volume. Quality over quantity, as the saying goes. Your best asset isn’t the size of your audience but your known users: resolved IDs and audience segments you can clearly identify, package, and sell to advertisers.
The majority of traffic is anonymous and unauthenticated, as we found in our State of Audience Data Monetization report with Digiday, making it nearly impossible to monetize at the rates your audiences should warrant. So when traffic declines and doesn’t recover, publishers who rely on volume for their programmatic revenue feel the impact right away. But those with known, addressable audiences can persevere and monetize their inventory more precisely and efficiently.
With this reality in mind, publishers can shift their goals away from increasing site sessions and instead focus on maximizing the revenue potential of the sessions they receive.
You Can’t Sell What You Can’t See
Before any AI or agentic solution can work, you need a unified view of who actually makes up your audience. Publishers have a wealth of rich first-party data available, but even if your platform gets thousands of daily visitors, fragmented identifiers alone do not form coherent, actionable profiles. Identity resolution using 1P attributes, 3P enrichment, authenticated identifiers, and inferred identifiers creates golden records: privacy-preserving, persistent, and unified accounts for every visitor.
Building a golden record is an essential part of an effective audience and monetization strategy centered around 1P data. Across programmatic, direct, curated, and agentic workflows, resolved IDs make it possible to build meaningful segments that clearly demonstrate audience quality to advertisers. Without this foundation, publishers are limited by what they don’t know and can’t accurately convey or monetize their premium audiences.
The More You Can Tell Your Advertising Partners About Your Audience, The More Valuable They AreTaking your known users to addressable audiences you can activate across platforms requires depth beyond your unified identity foundation. Layering in 3P enrichment transforms traffic into premium inventory; it’s the difference between someone who visits your site once and a homeowner between 35 and 44 years old in the market for a new car.
Publishers with an enriched identity graph have the option to create more specific, addressable audience segments, which in turn command higher CPMs. We’ve seen how appending resolved identifiers like UID2 to outgoing bids directly lifts programmatic revenue, with increases in CPM and addressability.
Manually building discoverable audiences from an enriched ID graph is possible but takes time, as Ad Ops teams can attest. But the industry is moving rapidly towards agentic workflows that are changing the game.
Instead of tediously combing through data after receiving an RFP, publishers can use tools like Optable’s Audience Agent to review the contents, search inventory, and compile new audience segments within parameters that prevent hallucinations. Those audiences can be packaged and activated across SSPs and ad servers from the platform, and the agent can even draft a response, saving teams the time and brain power they can better use for strategic initiatives.
The result is a monetization engine that runs on the audience you already have. With enriched, packaged audiences ready to go, AI can take it the rest of the way.
Stop Chasing Traffic and Start Selling Audiences
Traffic will always matter for audience monetization, but a strategy that depends only on volume is not viable in the age of AI. Thriving in this environment hinges on a concrete identity foundation and agentic layers that can assemble, activate, and sell audiences quickly and accurately.
The emerging agentic ecosystem will reward publishers who know their audiences, can package them precisely, and can sell them at machine speed. The tools to build that infrastructure and connect to the agentic ecosystem are available now.
Ready to get started? Schedule a demo.
Publishers are navigating a complex programmatic landscape across fragmented deal-making, AI disruption, and the continued pressure of walled gardens. Last month, Optable's VP of Product, Andy Sharkey, joined a lineup of industry leaders on The Pub Report’s latest webinar to dig into these challenges and what's actually being done about them.
Here's what stood out.
The Big Picture: No One Wins Alone
The through-line across every session was the importance of collaboration.
That spirit set the tone for a conversation that was less about abstract AI hype and more about practical applications that fit into the workflows publishers and buyers already rely on today.
"There's no better time than right now to be collaborating and coming together and talking about these key topics. No one is going to succeed on their own." — Rob Beeler, Beeler.Tech
Practical Applications of Agentic Advertising With Optable’s Andy Sharkey
Kicking things off, Andy made a compelling case for how agentic AI can ease one of programmatic's most persistent pain points: the operational burden of managing PMP and curated deals at scale.
As PMP and curated deals have become increasingly central to publisher revenue strategies, Ad Ops teams are feeling the pressure. Campaign planning is traditionally manual, slow, and fragmented. The process can't sustainably keep pace with demand.
One solution? A Sales Agent built to slot into the existing programmatic ecosystem without replacing the core workflows.
Andy demoed an example of this in practice using Claude, connected to Optable. Here’s how it can work:
- A buyer drops a campaign brief directly into the agent.
- The agent reads the brief, identifies relevant deal packages (for example: CTV and video inventory targeting specific demographics across web and mobile) and surfaces available options automatically.
- Once the buyer activates a deal, the agent finds the preferred SSP, generates a new deal ID, injects it into the SSP, and shares it with the buyer to load into their DSP.
The best part? It’s not science fiction. As Andy put it: "We're not talking about a complete revolution with AI. Publishers are going to continue with their SSPs and DSPs and partners for the foreseeable future. This is a technology layer we can introduce to help automate the creation of PMPs and curated deals."
On the publisher side, the agent gives teams control over how their inventory is represented, allowing them to define audience packages, set pricing, toggle on discovery for specific demographics, and manage authorized buyers. It's designed to be SSP-agnostic with potential for connectivity across the ecosystem.
Andy's takeaway for publishers was direct: make sure you're working with technology that gives you strong identity, contextual, and audience signals, and that your audience agent is compatible with the AdCP Signals Protocol.
Want to learn more about the emerging agentic advertising era and what it means for publishers? Download our guide here.
The Wider Conversation
Brian O'Kelley (Scope3) tackled the challenge of competing with walled gardens, which continue to attract advertisers because buying on them is often easier than navigating the open web. His vision leans into AI as a way to unlock new demand sources that include and go beyond traditional display while staying fully compatible with the programmatic infrastructure.
Dr. Paul Farrow (Microsoft) raised some of the most thought-provoking questions of the day around content monetization in the age of AI. When users get answers directly from LLMs without ever landing on a publisher's page, the traditional revenue flywheel starts to break. His proposal: the industry needs a systematic, marketplace-based solution to regain equilibrium for publishers of all sizes across the open web.
Scott Siegler (Amazon Publisher Services) rounded things out with a look at how the APS Prebid Adapter is helping under-resourced publishers access demand at scale, reducing the technology fragmentation and cost of ownership that hold smaller players back.
What This Means for Publishers
The tools to improve programmatic advertising are rapidly developing and evolving. The publishers who will benefit most are the ones actively working with the right technology partners to build the identity, audience, and contextual infrastructure that agentic workflows will depend on. We're proud that Optable's work is part of that conversation.
Ready to explore how agentic solutions can put your audience data to work and simplify your workflows? Book a demo today.
Rich signals, day one.
What teams actually need from an audience platform is simple: usable data. Ideally trusted and reliable.
Not in a few weeks. Not when integrations are built and tested. Immediately.
Because until you have enough signal to build and activate audiences, the platform isn’t doing much for you.
We’re closing that gap today with Optable Attributes. A collection of enrichment capabilities so you can start building rich audience segments from day one.
Optable Attributes is:
- Audience intelligence: Instant access to a catalog of high-quality consumer signals sourced from Optable 3rd-party data partners.
- Contextual intelligence: AI-driven content classification transforms page content into meaningful interest and intent segments.
- Ad intelligence: Real-time capture of ad delivery and auction signals to build audiences from real intent and actual value.
All delivered in a single package for one flat-rate fee.
It's what turns your identity graph into an audience engine, without the operational and cost overhead.
Audience intelligence
Start with a complete picture of your visitor
Your 1st party data may tell you who someone is, but it rarely captures the full picture of how they behave, what they buy, or what they’re likely to do next.
Audience Intelligence extends that view with a turnkey 3rd-party dataset available directly inside Optable. No need to source, clean, or integrate external data. It’s already structured and ready to activate.
This dataset includes multiple signal types, spanning:
- Transactional behavior and purchase patterns
- Spending power and propensity indicators
- Brand affinities and retail activity
- Lifestyle and interest-based signals
- Motivational and intent-based attributes
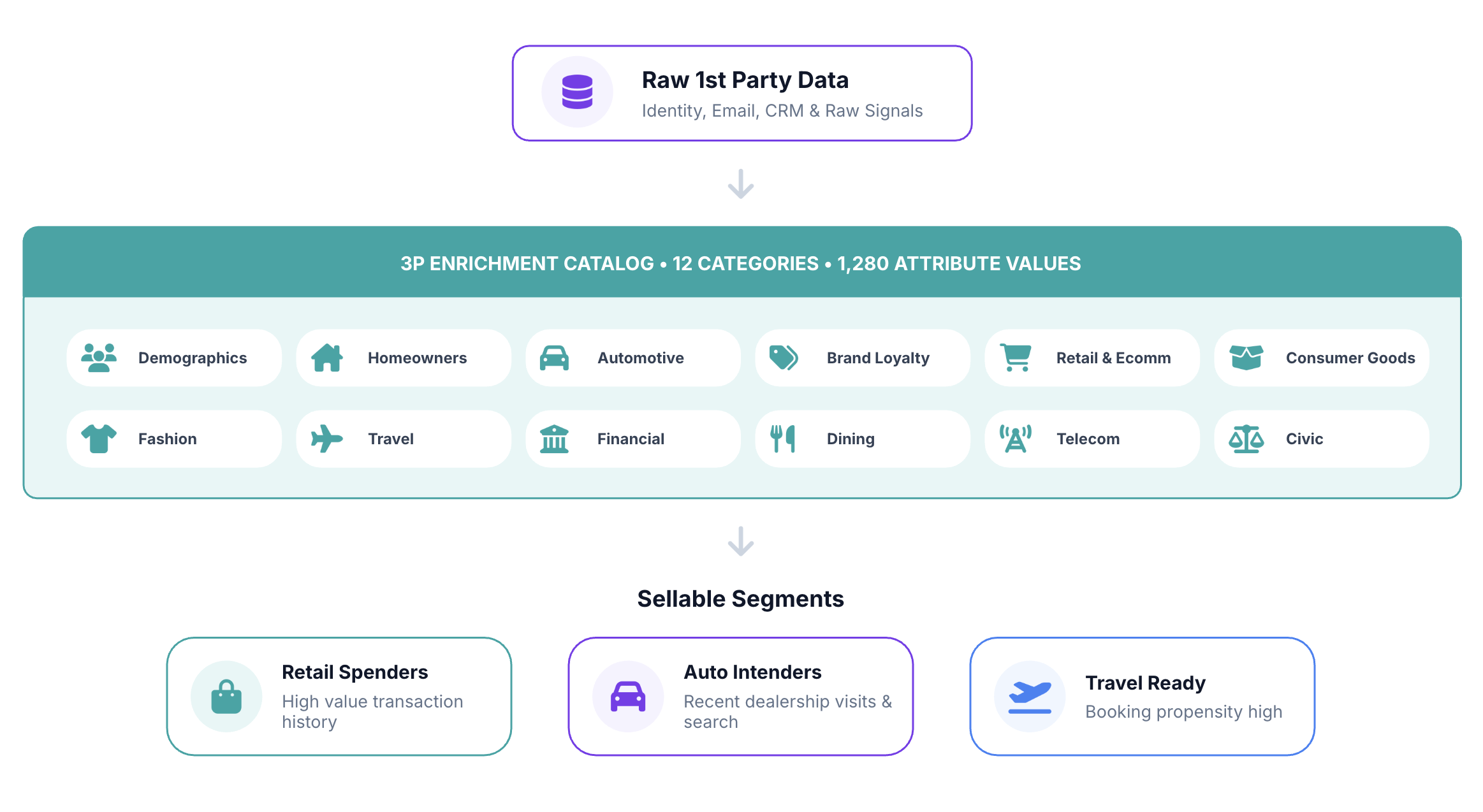
The result is a stronger foundation for both planning and monetization. Teams can move quickly from raw identity to defined, sellable segments like:
- “High-value retail spenders”
- “Auto intenders with recent purchase signals”
- “Travel-ready audiences with strong booking propensity”
Traditionally, this level of enrichment requires multiple providers, each with separate contracts and CPM-based pricing. Here, it’s delivered as a single integrated dataset under a flat rate, so usage isn’t tied to cost.
Contextual intelligence
Turn content into clear, reliable signals
Contextual data is often treated as a shortcut to intent, but most systems still rely on keywords and URL patterns. That approach misses nuance.
Optable Contextual Intelligence uses LLM-driven analysis to evaluate full page content and classify it based on meaning. Our semantic engine reads the content itself, not just metadata, and maps that understanding to standardized taxonomies.
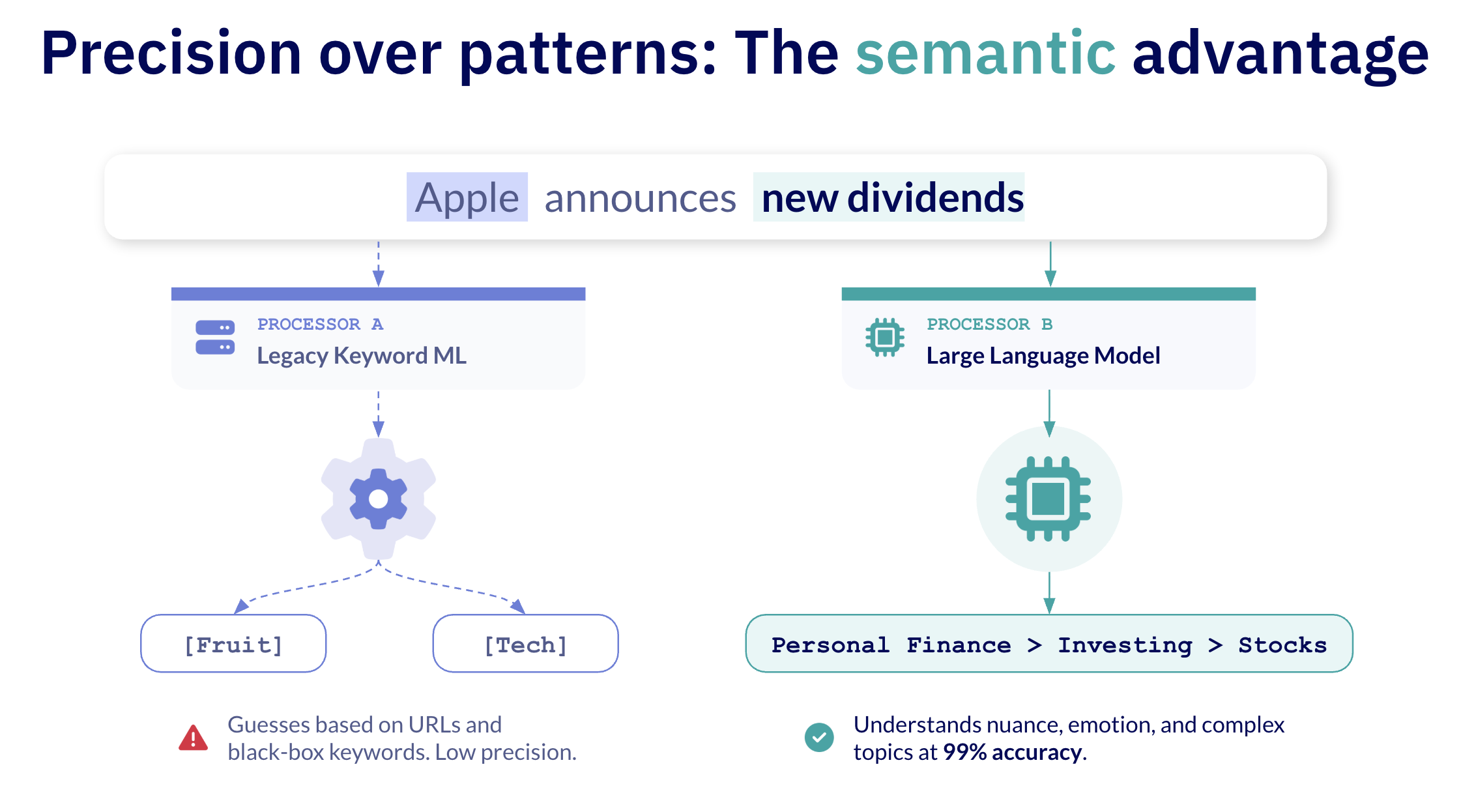
From there, it:
- Classifies content into IAB Content Taxonomy 3.1
- Extracts topics, entities, and intent signals
- Applies consistent categorization across content
- Links those signals directly to user identity
Instead of tagging pages in isolation, this builds a persistent view of what each user actually engages with over time.
That makes contextual data far more actionable. You can define audiences based on consistent behavior, not single page visits, and apply those insights directly to packaging and targeting.
It also removes operational overhead. There’s no manual tagging, syncing across vendors, and separate contextual systems to manage. The classification happens automatically and feeds directly into audience creation.
Ad intelligence
Use real buyer behavior as your strongest signal
Content suggests intent. Auction data shows how that intent is valued.
Most teams treat Prebid and GAM data as reporting, but it actually reveals something far more useful: How the market values your audience.
Optable captures these real-time signals including:
- Impressions, clicks, and viewability
- Bids, CPMs, and bidders
- Advertiser names, deal IDs, and bidding patterns
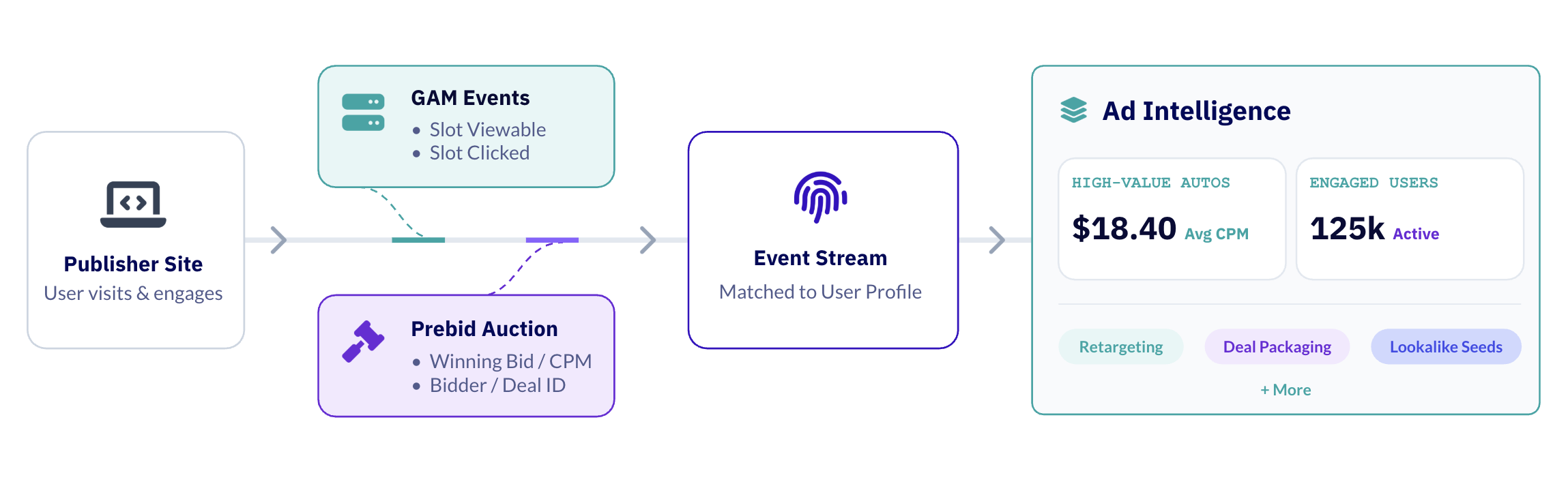
Once structured and tied directly to user records in the platform, this data becomes a valuable building blocks for segmentation.
You can build audiences such as:
- Brand loyalists: Users consistently targeted by a specific advertiser
- Vertical intent groups: Users bid on across a category like auto, travel, or finance
- High-value users: Users who consistently attract higher CPMs
These are demand-validated signals, reflecting what buyers are actually willing to spend against.
That opens up more direct ways to act on the data, from packaging PMP deals backed by bidder demand to identifying competitive targeting opportunities and building lookalike seeds from winning bids.
Instead of inferring intent, you’re working from observed market behavior.
Why our model is different
Most teams rely on a combination of point solutions to achieve anything close, namely:
- 3rd party data providers charging CPM-based fees
- A separate contextual vendor with CPM-based fees
- Internal tools or add-ons for auction analysis
Each solution has its own pricing model, integration requirements, and workflows. Bringing them together requires ongoing maintenance, with increasing cost and complexity as you scale.
Optable Attributes consolidates these capabilities into a single solution with:
- One system
- One workflow
- One flat-rate
Publishers and agencies get faster access to valuable signals, fewer dependencies across vendors, and a cost structure that doesn’t scale with volume.
The takeaway
Most platforms make you wait for your data to become useful. You deploy, collect signals, and gradually build toward something you can eventually activate.
Optable Attributes skips the cold start. You start with enrichment baked in across audience, contextual, and ad intelligence. So you can move directly into building, packaging, and activating differentiated audiences without delay.
At the same time, the economics are simpler. Instead of layering multiple vendors and CPM-based costs, you get a single system with predictable pricing and fewer moving parts.
And if you already have trusted vendors in place, Optable Attributes works alongside them, extending your current setup with additional signal and functionality.
Accelerating the path from signal to revenue, with less friction along the way.
Getting started
Optable Attributes is available now. If you are an existing Optable customer, speak with your account team about Optable Attributes today. Or to learn more, let's chat.
At the Digiday Publishing Summit in Vail, March 23-25, publishing decision-makers gathered to discuss the industry's most pressing challenges. Three days, three themes: organizational transformation, monetization in the post-search era, and the new economics of influence.
But throughout the summit, there was a common undercurrent: the industry has shifted, and the old playbook no longer applies.
Here's what we learned.
The Traffic Problem Is an Identity Problem
The theme of traffic decline and its impact carried over all three days of the event.
- Publishers have been dependent on search traffic to drive registrations, memberships, and ad revenue.
- AI results, algorithm updates, and platform volatility have all contributed to the erosion of search traffic.
- Declining traffic means fewer known users, which means a shrinking addressable audience for advertisers and subscription conversion.
- Publishers have to rethink their value proposition; users can find quick answers elsewhere, so publishers need to not only attract new visitors but give existing ones a reason to stick around.
The reality: Publishers who have been building identity infrastructure independent of traffic source are in the best position for every session to become an asset.
Subscriptions Work, But They’re Not for Everyone
The urgency around subscriptions dominated Day 1, but not without candid discussions about how challenging the pivot can be.
- Converting to a subscription model is a challenge and lengthy process that can risk hedging out loyal audiences.
- Most publishers cannot realistically compete with or achieve the same success as the NYT and WSJ in subscription wallet share.
- Social and off-platform audience building emerged as a parallel, which will require cross-channel attribution.
The underlying tension: Ad revenue and subscription revenue don't always play nicely. Paywalling content risks removing it from programmatic monetization.
AI Presents New Pressure and Opportunities
AI has moved beyond a buzzword, appearing across conversations as a challenge as well as a competitive tool.
- AI-generated answers capture search referral traffic at the top of the funnel.
- Unauthorized AI bots are crawling sites en masse, contributing to site downtime while attempting to monetize the information they’re ingesting.
- According to MuckRack’s State of Journalism 2026 report, 82% of journalists are using AI tools, and publishers are building editorial workflows with AI.
The opportunity: AI is forcing publishers to rethink content creation and distribution practices. But the same disruptive technology is also giving lean teams new tools to package audiences, respond to briefs, and unlock revenue that manual workflows couldn't reach.
The Monetization Gap is Widening, But the Toolkit is, Too
Day 2's monetization track fostered actionable conversations.
- Off-platform revenue is growing to complement on-site programmatic.
- Advertisers are consolidating spend into programmatic direct and PMPs, demanding precise audiences and proof of outcomes. This shift will reward publishers with strong first-party data infrastructure.
- Curation is gaining traction as publishers seek to reclaim control over how their inventory is packaged and sold.
- Agentic audience building and RFP response creation are starting to close the operational gap for smaller teams.
The consensus: Diversification isn't optional, but it requires the right technology and organizational readiness.
Where Do Publishers Go From Here?
The Digiday Publishing Summit made one thing clear: publishers are very aware of the challenges they’re facing, and they’re actively looking for answers. What they're short on is time, bandwidth, and the right infrastructure to act.
We’ll be publishing a series of posts going deeper into the practical paths forward on each of these themes, covering agentic audience monetization, AI-powered sales workflows, omnichannel diversification, and more.
Thank you to everyone who braved the winter storm to join us for Optable Connect in Toronto. While some of you were delayed or homebound due to weather, we’re so grateful for the amount of interest in our event and the future of AdTech.
Across the board, the theme of this year’s event is transformative: AI is here to stay, and the age of agentic advertising is already upon us.
We learned through live demos, active panel discussions, and a fireside chat that the industry continues to adapt alongside new and emerging technologies — and the companies evolving with agent-ready data, AI-powered strategies, and a collaborative mindset are the ones most likely to succeed.
For now, we’re sharing the highlights, key concepts, and action items from Optable Connect 2026 to empower your teams and activate your data.
The Big Picture: Agentic Infrastructure + AI Readiness
Optable’s CEO, Vlad Stesin, opened by honing in on the ongoing disruption and transformation of the media landscape. He discussed how, as AI evolves, challenges like privacy and fragmentation across tools and data become more apparent.
While AI presents new obstacles for publishers, platforms, advertisers, and agencies to overcome, it also poses unique opportunities for collaboration. To make the most of the agentic, AI-powered era we’re entering, media buyers and sellers can work together to activate engaged audiences outside of walled gardens, creating a future of targeted, data-driven advertising.
We welcomed representatives from all parts of the ecosystem to share their thoughts and learn from one another. Over the course of the day, we heard new perspectives and actionable insights for the agentic advertising era that publishers, advertisers, agencies, and media companies need to know.
If you missed out on the live event, you’re in the right place. We’ll walk through the highlights from every session and tie it all together at the end.

1. From RFP to Activation: A Deep Dive into Agentic Advertising with Live Demo
To kick things off, Bosko Milekic, Co-Founder & CPO of Optable, helped us get familiar with the growing applications of agentic AI in audience planning as the demand for PMP increases.
He discussed how manually planning campaigns is slow, fragmented, and tedious. With varied or incomplete publisher data, a lengthy proposal process, and the risk of user error, responding to an RFP the old-fashioned way takes too much time for inconsistent results.
But that all stands to change when you integrate AI agents into your workflow.

Bosko reintroduced us to Optable’s Audience Agent, previously named the Planner Agent — an agentic tool built to sift through your structured data, uncover new audiences, and simplify the proposal process so you can activate audiences faster and more effectively. With a quick demo, Bosko showed how quick and easy it is to prompt the agent, generate relevant insights, and draft an RPF response using the data in the Optable platform.
He brought his presentation home by debuting Optable’s Sales Agent (in beta) and offering a bold proposition: a future of agent-to-agent (A2A) collaboration between publishers and advertisers. Optable is working towards facilitating an agentic marketplace, automating the media selling process while enriching audience data for more optimized revenue generation.
2. Agentic Advertising Perspectives: How Can Agentic Build On and Enhance Our Existing Infrastructure?
Moderator: Vlad Stesin (Optable)
Speakers: Pierre-Luc Hardy (Triton Digital), Sonia Carreno (IAB Canada), Alex Gardner (Index Exchange), Scott Menzer (Unity)
This discussion dove into the applications of agentic AI in programmatic advertising, expanding on themes of:
- Industry alignment: It’s not enough for AI to keep advancing. The industry needs to collaborate and agree on AI standards and practices to improve results, preserve data privacy, and maintain transparency.
- Interoperability before automation: Agent-ready data and infrastructure need to come first to ensure a smooth transition to agentic use applications and, ultimately, agent-to-agent transactions.
- Human oversight: There are clear benefits to automating workflows, but at the end of the day, human buyers have the experience and expertise to know best.

3. Signals + AI = Intelligence: How Publishers Are Updating Their Audience Strategy in the Age of AI
Moderator: Patrick Viau (Optable)
Speakers: Geoffrey Bernard (LaPresse), Julie Kerr (CBC), David Lundell (Hearst), Scott Bender (Newton Research)
Our guests put AI in context for publishers on the front lines, exploring what it actually takes to compete in an AI-driven advertising world. Themes included:
- Foundation before automation: AI-readiness requires a clear data infrastructure, solid identity strategy, and clean first-party signals. Publishers without that foundation will struggle to make the most of AI tools.
- Competing with walled gardens: Publishers with AI-ready data can continue offering advertisers trust and transparency and provide advanced targeting and measurement to better rival the appeal of walled gardens.
- People alongside data: Empowering revenue and operations teams with the right AI tools before implementing new technology is what drives real impact.

4. Fireside Chat: The Importance of Data in the AI Age
Host: Vlad Stesin (Optable)
Guest: Benjamin Webb (Above Data)
In this interlude, Vlad and Ben started by soft-launching a partnership between Optable and Above Data. They spent their conversation emphasizing what it means to have AI-ready data and what publishers and platforms need to prioritize before adopting agentic AI. They covered:
- Advertiser appeal: With agentic AI, publishers can enrich their first-party data and deal directly with advertisers, offering an attractive alternative to saturated walled gardens.
- Data preparedness: AI-ready data needs to be structured, enriched, standardized, and queryable by agents. Data that doesn’t meet these criteria will only impede performance.

5. How Will AI-Powered Solutions Change Media Buying in 2026?
Moderator: Vlad Stesin (Optable)
Speakers: Alex Feldman (Havas), Andrea Kwiatek (Goodway Group), Adiela Aviram (Manulife)
The final panel of the day brought a candid demand-side perspective covering where agencies and advertisers are in their AI journeys and what it will take to move forward with confidence and profitable results. They covered themes like:
- Urgent standardization gap: Publishers and platforms need to agree on AI standards for the tools to work efficiently and effectively across the entire ecosystem. The production of disparate tools creates fragmentation before the industry can develop frameworks.
- AI needs human oversight: Human expertise should continue informing and reviewing AI workflows. Automating everything with no oversight will create new problems.
- Garbage in, garbage out: Data quality directly impacts results. Panelists agreed that partners need to be upfront about their data limitations or polish their data beforehand.

Key Takeaways
Throughout the day, recurring themes emerged, allowing us to pinpoint what is top of mind for industry experts:
- Agentic advertising is already here: It’s not an upcoming trend. Agencies are using AI agents to plan, execute, and iterate on campaigns. Publishers are adopting agentic AI for identity management and audience creation.
- Your data needs to be AI-ready: Structured, enriched, and organized data is essential for agentic AI to perform accurately and efficiently. AI readiness is a prerequisite if you want to take advantage of agentic workflows.
- Standards and interoperability aren't optional: Multiple AI frameworks are emerging, and the industry needs to align on how they work together to mitigate fragmentation.
- Human oversight is essential: Publishers and advertisers know best; while agentic AI can speed up timelines and make use of existing data, the AI can inadvertently cause other issues. Monitoring AI output should continue for quality assurance.
- You can compete with walled gardens: Major platforms like Meta and Google are oversaturated. Agentic opportunities could allow AI-ready publishers to gain a critical advantage with unique first-party data, engaged audiences, and streamlined sales.
What’s Next
The foundation for agentic advertising needs to be built now, not later.
For the industry at large, the urgency centers around agreeing on standards like AdCP and IAB Tech Lab's Agentic Roadmap, and the window to get ahead of fragmentation is getting smaller. For organizations ready to move forward, it’s time to audit your data readiness, identify use cases to test, and put structures in place so you can scale confidently.

As for the Optable team, we’re here to help publishers and their partners succeed in the agentic era by making data, AI, and standards work together in practice so they can monetize more effectively with the tools — and data — at their disposal.
- We'll continue investing in the data infrastructure and identity foundations that make agentic advertising possible.
- We'll keep building toward agent-to-agent collaboration and seamless cross-system buying workflows by building upon the Audience Agent's ability to surface audiences and draft proposals.
If you joined us in Toronto, thank you for the enthusiasm and candid discussions. If you couldn't make it, we hope this recap gets you up to speed — and we'd love to keep the conversation going at our event in New York City later this year.



.png)


.png)
.png)








